Do you know what Vortex Ransomware is?
Vortex Ransomware is an infection that appears to have been targeted at users who live in Poland. Once this infection slithers in and encrypts your personal files, it creates a file that represents a ransom message in Polish. Of course, different versions of this infection could be created depending on your geographical location. According to our research team, the threat can connect to a remote server (for example, wielkijopl.temp.swtest.ru) to determine your IP. Notably, this IP is represented via the ransom note. All in all, it is possible that the threat will determine your geographical location before it creates the ransom note. In any case, the name of the infection – which, by the way, is represented via the ransom note as well – will not change, and that should help you identify the threat. We strongly advise removing Vortex Ransomware from your operating system as soon as possible, but read the report first to learn more about the activity of this dangerous threat.
According to our research, spam emails could be employed for the distribution of Vortex Ransomware. As some might know, this distribution method has been used to spread Enjey Crypter Ransomware, Redants Ransomware, Wallet Ransomware, and many other recently discovered threats. If the .exe file of this threat is executed successfully – and that is most likely to be done without your notice – the data of your personal files will be modified, and the names will gain an additional extension, “.aes”. According to the ransom note, the files are encrypted using the AES-256 encryption algorithm. At the time of research, the threat was only capable of encrypting image files, but it is likely that Vortex Ransomware will be updated to target different kinds of files, if that has not happened already. Can you recover your files by deleting the ransomware? Unfortunately, you cannot do that, and cyber criminals are banking on that to make you pay the ransom fee that is demanded from you via the ransom file.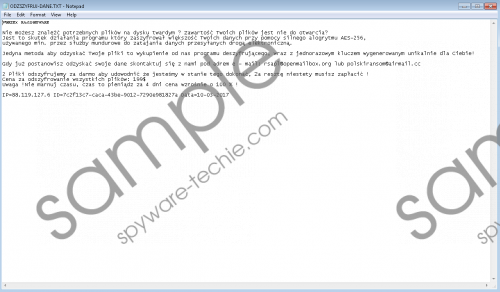 Vortex Ransomware screenshot
Vortex Ransomware screenshot
Scroll down for full removal instructions
“ODZSZYFRUJ-DANE.TXT” is the file used by Vortex Ransomware to introduce you to the ransom demands. Here is an excerpt from the message.
Jedyna metoda aby odzyskać Twoje pliki to wykupienie od nas programu deszyfrującego, wraz z jednorazowym kluczem wygenerowanym unikalnie dla Ciebie!
Gdy już postanowisz odzyskać swoje dane skontaktuj się z nami pod adrem e - mail: rsapl@openmailbox.org lub polskiransom@airmail.cc
You are asked to email rsapl@openmailbox.org or polskiransom@airmail.cc if you want to get your files decrypted. So, what happens if you contact any of these emails? Obviously, you will not be provided with a file decryptor right away, and you are informed about that via the ransom note. You are informed that you need to pay a ransom of 199 USD to get the decryptor. The note also informs that the price will go up in four days. So, should you pay the ransom fee? Considering that cyber criminals are the ones who are requesting this, you need to remember that they could fool you. There is always a chance that if you pay the ransomware quested by Vortex Ransomware, the decryptor will not be given to you. Whether you lose your files or recover them by paying the ransom (which is not guaranteed) or using backups, you need to delete Vortex Ransomware from your operating system as soon as you can. Use the guide below, or install an anti-malware tool, which we recommend because it can guarantee full-time protection as well!
Remove Vortex Ransomware from Windows
- Launch Explorer by tapping Win+E keys.
- Enter %USERPROFILE%\Downloads\ into the bar at the top.
- Look for the malicious .exe file. If found, right-click and Delete the file.
- Also, check the %TEMP% directory for the malicious file. Delete it if found.
- If you cannot find the launcher, install a malware scanner to help you out.
- Delete the ransom note file called ODZSZYFRUJ-DANE.TXT.
- Empty Recycle Bin and then perform a full system scan.
In non-techie terms:
Vortex Ransomware is an infection that requires immediate removal. This infection was designed to take your files hostage and demand a ransom in return of a decryptor that allegedly can help you decrypt them. It is unknown whether or not the creator of this threat would provide its victims with a decryptor, and so paying the ransom is, of course, risky. Whatever happens, you need to delete Vortex Ransomware from your PC, and you can do that in several ways. Most users are interested in manual removal (see guide above) because they do not want to invest in automatic malware removal software. Although you might be able to erase this threat manually, you also need to think about your virtual security. Clearly, something is wrong because the ransomware has managed to slither in. Therefore, we advise utilizing anti-malware software that can simultaneously eliminate malicious infections and continuously guard your operating system against malware. If you have more questions, use the comments section below to contact us.
