Do you know what slaker@india.com Ransomware is?
Our researchers say that if slaker@india.com Ransomware attacks you, there is a chance that you will lose all your files except your Microsoft programs and OS files. This includes all your photos, videos, audios, archives, databases, and even your executable files. Hopefully, you have a backup stored somewhere safe so that you can recover at least some of your important files. It seems that this new danger is indeed a new variant of a previous hit called "BTCWare Ransomware," which was cracked by malware hunters who came out with a free decryption tool. This tool may still be available and it might work in this case, too. But we do not advise you to go for it unless you are skilled enough. The only way for you to restore your computer is to remove slaker@india.com Ransomware right away. Please read our full report to understand how this dangerous program may have entered your PC and how you can avoid similar attacks.
When a ransomware program like this manages to sneak onto your system, it is quite likely that you have opened a spam e-mail recently. This malware infection can travel as an attachment disguised as an image, a text document, or a .zip archive. You may think that you would never open a spam mail and that it is easy to spot. Unfortunately, experience shows that still a lot of people can be made curious enough to want to open such a mail and view its attachment. This spam may claim that it is about a hotel booking where you gave wrong credit card details, an unpaid invoice, or even an unpaid parking ticket. It can be anything that could make you want to open it. The sender is usually a name and e-mail address that can appear to be authentic and believable. No wonder why so many people step right into this trap. Please note that most of the time it is not possible to delete slaker@india.com Ransomware or any other ransomware infection without having your files encrypted.
Yet another way for you to infect your computer with ransomware is to forget about updating your browsers and drivers (Java and Adobe Flash Player). Cyber criminals can set up websites using so-called Exploit Kits, which can take advantage of outdated software versions and their security holes to drop infections behind your back. This means that you could get redirected to such a malicious page after clicking on corrupt third-party ads or compromised links, and once the page loads, an infection like slaker@india.com Ransomware could be dropped without your knowledge. This is why you need to avoid clicking on suspicious content and update your programs regularly if you do not want to delete slaker@india.com Ransomware or any other threats from your computer.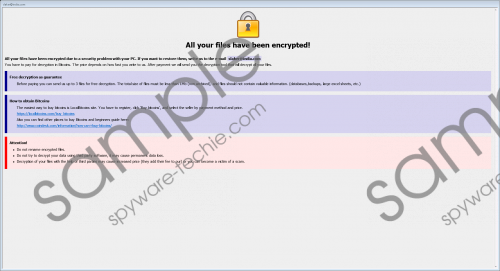 slaker@india.com Ransomware screenshot
slaker@india.com Ransomware screenshot
Scroll down for full removal instructions
This dangerous malware infection can virtually encrypt all your files except Microsoft programs and your OS files. Clearly, this could cause unbelievable damage. If you are interested, you can list all the encrypted files if you search for the ".[slaker@india.com]-id-AD0.wallet" extension. This way you can have an idea of the extent of the devastation. This threat drops a special ransom note file called "payday.hta" in your "%APPDATA%" folder as well as a text file ("! How Decrypt Files.txt") in all the folders where file have been encrypted. The text file is rather short and simply tells you that your files have been encrypted and you have to contact your attackers via slaker@india.com for the decryption.
The other file (.hta) comes up on your screen after the encryption and tells the same story but in slightly more details. You are not informed about how much you will have to pay for the decryption; only that you need to pay in Bitcoins, as usual. When you send an e-mail to these criminals, you can also attach up to three files that cannot exceed 1MB. You can have these files decrypted for free as a proof that these crooks can actually decrypt all your files if you pay. However, it is always risky to pay since criminals tend to disappear right after they receive the ransom fee. On the other hand, it is as good as supporting cybercrime. We advise you to remove slaker@india.com Ransomware as soon as possible.
Please follow our guide below if are ready to eliminate this severe threat from your system. Please note that this removal requires deleting certain registry Run keys as well. Editing the registry has its own risks if done by inexperienced users. If you do not want to use our guide and would like a more efficient automatic method, we recommend that you install a reliable malware removal program, such as SpyHunter.
Remove slaker@india.com Ransomware from Windows
- Tap Win+R and enter regedit. Press OK.
- Delete these registry keys:
HKCU\Software\Microsoft\Windows\CurrentVersion\Run::1payday
HKCU\Software\Microsoft\Windows\CurrentVersion\Run::2baby
HKLM\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run::3payday
HKLM\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run::4baby - Close the editor.
- Tap Win+E.
- Delete the malicious file you saved and launched.
- Bin the ransom notes: "%APPDATA%\payday.hta" and "! How Decrypt Files.txt"
- Empty your Recycle Bin and reboot your PC.
In non-techie terms:
When slaker@india.com Ransomware finds a way to penetrate your system, you can prepare to say goodbye to all your files practically. This new vicious program is indeed a new variant of "BTCWare Ransomware," which is only different in a small detail, the contact e-mail address the attackers use for the victims. You are offered to send three small files to be decrypted for free so that you can see that these cyber crooks do have the decryption key. In a reply message you are supposed to get further detail regarding the payment because the ransom note itself does not disclose too much. Since the predecessors of this new threat were cracked and a free tool surfaced to recover victims' files, you might be able to use it in this case, too, or wait for a while for a new one to be released. Still, it is important that you remove slaker@india.com Ransomware from your system immediately. If you would like to defend your PC against similar threats, we suggest that you install a reliable anti-malware program.
