Do you know what Search.myrecipesxp.com is?
It is possible that you are interested in cooking and therefore you would be glad to find Search.myrecipesxp.com search engine in your browsers, but we must warn you that this may not be a reliable tool. In fact, our researchers have classified it as a browser hijacker because of its capability to promote this search engine by setting it as your home page, default search provider, and even your new tab page. Virtually, this hijacker takes over the control of your browsers. It may also happen without your knowledge, which makes this malware infection intrusive and illegal, too. Do you think it is a good decision to leave this hijacker on your computer if its origin is rather questionable? What if it starts to function unexpectedly and you become exposed to dangerous third-party content? We believe that you should remove Search.myrecipesxp.com because it will just cause more security-related issues for you.
It seems that this infection attacks your computer through bundled malicious installers. If you have such a bundle on your PC, it can only mean one thing: You have visited suspicious freeware or torrent sites recently. It is possible that you did not even knowingly download anything, but simply clicked on a third-party advertisement, either a banner ad or a pop-up ad, and that resulted in an infected software package being installed in the background without your noticing it. Now you may think that you did not even click on ads. However, did you know that some ads are so “sophisticated” that they can disguise themselves as buttons and like a chameleon they can seem to be part of their environment? So it is quite possible that you think you click on a download button and seemingly nothing really happens. But you may also get redirected to other questionable websites on new tab pages. If any of this rings the bell, you should delete Search.myrecipesxp.com and run a malware scan on your computer to identify all possible threats as well.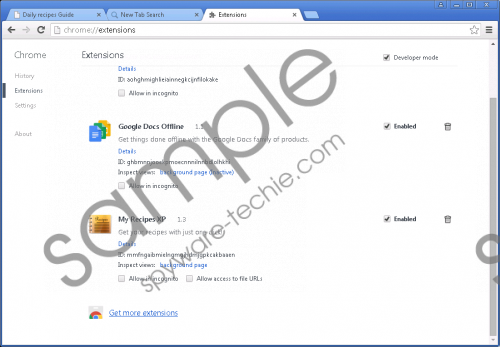 Search.myrecipesxp.com screenshot
Search.myrecipesxp.com screenshot
Scroll down for full removal instructions
Since it is quite likely that your system is also infected with adware on top of this hijacker, you need to know that you are never safe while surfing the web because these infections can hijack even legitimate advertisements. This means that you think you are on a reputable website like YouTube or Amazon and therefore the ads you find there are also trustworthy. However, these malware programs are capable of redirecting you to malicious websites even from these seemingly legitimate sites. If you want to find out if you have any adware or hijacker on board, you can open the list of installed programs in Control Panel or the extension lists in your browsers’ setting menu. Of course, the best solution is to use a reliable antimalware application that can detect all existing malware infections and not only the more conspicuous and visible ones, of course.
It is advisable to stay away from this search engine because our researchers have found it identical to Search.yourspeedtestnow.com and Search.myshoppingxp.com, which are also useless and potentially harmful browser hijackers. Just like all the other clones, Search.myrecipesxp.com also uses the same server (extsearch.maxwebsearch.com) to send your web search request to first. Then, you will be redirected to a potentially modified Yahoo! search results page, which may be filled with unreliable third-party sponsored links and ads. Here is what the Terms of Use says about this:
Using the My Recipes XP Software, you may encounter Third-Party Software that may be deemed offensive, indecent or objectionable. Nevertheless, you agree to use the My Recipes XP Software at your own risk and that My Recipes XP shall not have any liability to you with respect to such content.
Obviously, this search engine tries to make money for its creators through marketing affiliated third parties, i.e., routing web traffic to their websites. That is why you should never use this tool for web search because you might end up on malicious websites that could harm your system security more than it has been already harmed.
However, this is also why you should be more careful and make sure you know exactly what you are downloading and installing. In other words, it is worth performing a web search every time you want to download free software. In this case, for example, you could see in a few seconds that all search results are practically about why you should remove Search.myrecipesxp.com. If you confirm that your target application is clean, you should make sure that the website you want to download it from is a trustworthy one or not. This way you can save yourself some future headaches.
So here is what you can do to secure your computer after being infected with Search.myrecipesxp.com browser hijacker. First, you need to uninstall the application via Control Panel. Second, you need to reset Mozilla Firefox and Google Chrome in order to undo all the changes this hijacker made. Please follow our guide below if you do not know how to do that. Also, remember that your PC will only be fully safe if you eliminate all the threats. We recommend that you protect your computer with a reliable antimalware application.
Search.myrecipesxp.com Removal from Windows
Windows XP
- Click the Start button and open Control Panel.
- Select Add or Remove Programs.
- Click on the program and press Remove.
Windows Vista and Windows 7
- Press the Windows button and pick Control Panel.
- Click Uninstall a program.
- Click on the program and press Uninstall.
Windows 8, Windows 8.1, and Windows 10
- Press Win+I and open Control Panel.
- Select Uninstall a program.
- Click on the program and press Uninstall.
How to reset your browsers
Mozilla Firefox
- Press Alt+H and choose Troubleshooting Information.
- Press Refresh Firefox.
- In the confirmation window, click Refresh Firefox.
- Click Finish.
Google Chrome
- Press Alt+F and choose Settings.
- At the bottom, click Show advanced settings.
- Scroll down and click Reset settings.
- Press Reset.
In non-techie terms:
Search.myrecipesxp.com is an unreliable and potentially dangerous search engine that you should never use. Since this engine will be set as your home page, new tab page, and search engine in your browsers, it has been labeled as a browser hijacker. Using any of the third-party services and websites this tool offers to you could put your virtual security at risk. It is also likely that this is not the only malware threat right now on your computer. Therefore, we advise you to use an automated malware removal tool to detect and remove all infections, including Search.myrecipesxp.com.
