Do you know what Ramachandra7@india.com Ransomware is?
Currently, it is impossible to decrypt data enciphered by Ramachandra7@india.com Ransomware. Even though, cyber criminals who distributed the malware might suggest you purchase the decryptor from them, we strongly advise against it. The fact is that you cannot know if this tool exists at all or if they will bother to send it once the payment arrives. Therefore, if your savings is not something that you would like to risk losing, we advise you to get rid of the malicious application and get a fresh start. The removal guide that we placed at the end of the text will show users how to erase the malware on their own. Also, if you are still wondering how this could happen to you, we recommend reading the article to learn more about the threat.
The cyber criminals who spread Ramachandra7@india.com Ransomware have their ways to convince inexperienced users to open infected files. These files might be distributed through Spam emails, or they could be shared on unreliable web pages. Either way, it might have happened because you were not careful enough and the system was probably vulnerable to threats too.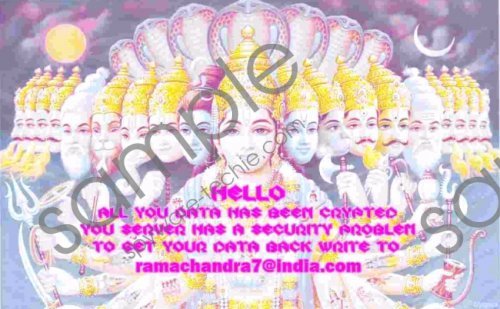 Ramachandra7@india.com Ransomware screenshot
Ramachandra7@india.com Ransomware screenshot
Scroll down for full removal instructions
Could it be that you occasionally download freeware or other suspicious data from the Internet and email? From now on, you should be extra careful if you do not want to experience what it is like to infect the system with threats such as Ramachandra7@india.com Ransomware again. Keep it in mind that even data that looks harmless could be malicious. For instance, the malware’s creators could distribute it with files that look exactly like PDF or other documents. To protect the system, you should either scan such files with a security tool or avoid opening them.
Furthermore, the malicious application was created while using the CrySIS Ransomware engine. There are lots of other similar applications that were developed with this engine. For example, we could mention such infections as Meldonii@india.com Ransomware, Makdonalds@india.com Ransomware, Okean-1955@india.com Ransomware, Alex.vlasov@aol.com Ransomware, and may other ones. Just like these mentioned threats, the malware could also encrypt both personal and program data on the PC. Each enciphered file should have a similar extension to the following one: .id-B4500913.{Ramachandra7@india.com}.xtbl. The only data that should remain unaffected would be files of your operating system.
After the encryption, Ramachandra7@india.com Ransomware might change your Desktop picture with a JPEG file called how to decrypt your files.jpg or place a text document called Decryption instructions.txt. Neither of these files actually contain instructions as they simply require you to email the cyber criminals. Their response should provide instructions on how to purchase the decryption software. However, as we mentioned in the beginning, buying it could be rather risky as you may send the money and never receive the decryptor.
Needless to say that we recommend users to get rid of the threat at once. Ramachandra7@india.com Ransomware is not a program that you could remove through Control Panel. Unfortunately, its deletion is more complicated than users might have imagined. Thus if you made up your mind to eliminate it manually, at least use the removal guide placed below this text. It will list all paths where particular data needs to be erased. Nonetheless, if you fear that this task might be too complicated for you, try to use a legitimate antimalware instead. It would allow the user to locate and erase the threat automatically. We should also mention that, if you saved some copies of data somewhere else besides the infected computer, you should be able to recover it with no trouble.
Delete Ramachandra7@india.com Ransomware
- Launch the Explorer by pressing Windows Key+E.
- Find and erase executable files with random titles from the listed directories:
%ALLUSERSPROFILE%\Start Menu\Programs\Startup
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup
%USERPROFILE%\Microsoft\Windows\Start Menu\Programs\Startup
%ALLUSERSPROFILE%\Microsoft\Windows\Start Menu\Programs\Startup
%ALLUSERSPROFILE%\Application Data\Microsoft\Windows\Start Menu\Programs\Startup
%WINDIR%\Syswow64
%WINDIR%\System32 - Close the Explorer.
- Press Windows Key+R, type regedit and select OK.
- Go to the following directory: HKCU\Control Panel\Desktop
- Locate a value name called Wallpaper.
- Right-click the value name, select Modify and replace how to decrypt your files.jpg with a different picture.
- Navigate to this path: HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Wallpapers
- Find a value name called BackgroundHistoryPath0.
- Right-click the value name, select Modify and replace how to decrypt your files.jpg with another wallpaper.
- Find this directory: HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- Locate value names with random titles; their value data should point to %WINDIR%\Syswow64\*.exe and %WINDIR%\System32\*.exe
- Right-click these value names separately and select Delete.
- Close the Registry Editor and empty Recycle Bin.
In non-techie terms:
The malicious program is only one of many almost identical threats that were created recently. It settles in the system by creating executable files with random titles. Additionally, it could also modify some data on the system as well. As a consequence, deleting the malware manually might be a hard task for inexperienced users. Therefore, it might be easier to get a trustworthy antimalware tool and allow it to eliminate Ramachandra7@india.com Ransomware.
