Do you know what Parisher Ransomware is?
If Parisher Ransomware finds a way to your computer, it could cause you severe headache since it encrypts all your documents. You can only see your files again if you pay the ransom fee, which is, in this case, very high. In fact, this fee is so high that most likely only companies would have this kind of capital to transfer in the hope of being able to recover their files. Unfortunately, this ransomware program uses an algorithm that is unknown; therefore, you cannot find free tools on the web yet to restore your files for free. You can only be saved actually if you have a recently made backup copy stored on a portable drive. But even if you have this copy, your first move should be to remove Parisher Ransomware from your system. Our researchers say that it is not too difficult to eliminate this threat but prevention should be your priority if you do not want to have further malware threats endangering your virtual world and your data. Please read our full report on this dangerous ransomware to learn more about the risks and solutions.
Most ransomware infections infiltrate your system via spam e-mails or Exploit Kits, but not this one; at least, not yet. Right now, according to our researchers, this malware program is mostly spread through remote desktop protocol and related software, including TeamViewer. This means that your computer could be the part of a company network and the system administrators can access your computer via such protocol. However, cyber criminals can somehow exploit certain weaknesses, such as easily hackable passwords or configurations, and gain access to your system as well as the whole network. This means that a whole company LAN (Local Area Network) could be infected with this vicious malware in no time. This is one reason why we believe that this ransomware could be targeting corporations.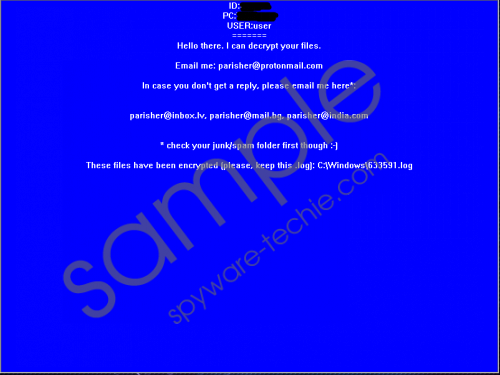 Parisher Ransomware screenshot
Parisher Ransomware screenshot
Scroll down for full removal instructions
But it is quite possible that these criminals will change tactics to distribute Parisher Ransomware more widely. Therefore, you might find it spreading in spam e-mails and by Exploit Kits as well. We suggest that you be more careful when you are checking your mails even in your inbox because modern spam mails can easily end up there. These spams may use totally legitimate-looking sender addresses, for example, and believable subjects that could draw your attention right away. There are usually three clicks involved in a spam attack. First, you open the mail. Second, you feel the need to click on the attachment to save it. And, finally, you click to open the attached alleged overdue invoice. However, by the time you realize that the attached file is fake or wrong, all your files will have been encrypted. If you delete Parisher Ransomware at this stage, there may be no way for you to restore your files.
Our research shows that this ransomware is a new version of the well-know threat called Mobef Ransomware. This infection encrypts your text files, including .docx, .pdf, .txt, .xml, and more. Unlike most of other ransomware programs, Parisher Ransomware does not alter your file names and does not add a unique extension to them either. Before changing your desktop background with its ransom note window, it also drops a number of files onto your system. For example, "HELLO.0MG” and "LOKMANN.KEY993” into all subfolders of %USERPROFILE% as well as a log file that contains the list of the affected files called "[6-digit ID].log” in your %WINDIR%. The 6-digit ID you will see in the ransom note that actually comes up moments after the encryption is over.
The ransom note has a blue background that looks very much like the infamous blue screen of death. This note does not tell you too much about this attack and the payment method. All you learn is that you have to send an e-mail to these crooks using parisher@protonmail.com. If you do not get a reply, you are also given three more alternative addresses to use. We have information about a user who claims that he contacted these criminals and they demanded 5 Bitcoins for the recovery of his files, which is around $3,200. We do not think that every computer user could easily pay this amount. The usual rate ranges from 0.1 to 1 BTC. This amount is totally insane; therefore, we do believe that it is meant for companies. In any case, if you find this beast on your computer, you need to act quickly and remove Parisher Ransomware.
Please follow our guide below if you want to take matters into your own hands. It is not impossible to delete this malware program even if you are not an experienced user. It is also possible that this is not even the only threat on your system; however, it is definitely the most severe one. We hope that you see how easy it is to let such dangerous threats onto your system. If you want proper protection against all kinds of malware invasions, we suggest that you download and install a reliable anti-malware product, such as SpyHunter. If you need assistance to remove Parisher Ransomware, please leave us a message below.
Remove Parisher Ransomware from Windows
- Tap Ctrl+Shift+Esc simultaneously to open Task Manager.
- Locate the malicious process, right-click on it, and select Properties.
- On the General tab, identify the Location of the executable (e.g., %APPDATA%, %TEMP%, and %LOCALAPPDATA%).
- Kill the malicious process by clicking End task.
- Bin "HELLO.0MG" and "LOKMANN.KEY993" from every %USERPROFILE% subfolders.
- Delect the log file from %WINDIR%
- Empty your Recycle Bin and reboot your system.
In non-techie terms:
Parisher Ransomware is a malware infection that you must take very seriously because if this threat manages to sneak onto your system, you can virtually say goodbye to all your documents. The cyber criminals behind this attack seem to have set a very high ransom fee in exchange for your decryption key and software. If you are ready to pay around $3,200, of course, there is no problem for you, as long as you get something for your money. You may not know but cyber criminals are not famous for keeping their words. Also, technical issues may emerge that could stop you from getting your decryption key from the remote Command and Control server. Therefore, we suggest that you remove Parisher Ransomware as soon as possible. If you want to protect your system from similar dangers, you may want to consider installing an authentic anti-malware program.
