Do you know what Opencode@india.com Ransomware is?
Opencode@india.com Ransomware’s primary objective is to encrypt your personal files and offer you to buy the decryption tool to get them back because once the files are encrypted you will be unable to access them. You can risk paying the ransom and not receiving the promised decryption key, so we suggest that you remove it entirely. In this article, we will discuss the most relevant information about this infection regarding its distribution, functionality, and removal in particular. If your PC has been infected with this malware, then read this whole description.
This newly released ransomware does not lock the screen like some other ransomware’s do. Rather, it is configured to encrypt your personal files with a very strong RSA-2048 encryption algorithm. RSA is a cryptosystem that is widely used for secure data transmission. In this cryptosystem, the decryption key is private and differs from the public encryption key. Hence, without the private decryption key, you cannot decrypt the public encryption key. The encryption key is 2048 bits long, so it is very difficult to decrypt using third-party tools. During the encryption, the decryption key is sent to the Command and Control Server set up by this ransomware’s developers. Also, it appends the encrypted files with an extension (e.g. .id-B4500913.{opencode@india.com}.xtbl) which contains an ID number and the email address that you have to write to in order to receive instruction on how to pay the ransom. Although the payment method and the amount to be paid are not known, we think that the criminals will demand that you pay in Bitcoins because the authorities will be unable to track the transaction. In any case, the criminals are not based in The US so prosecuting them might not be possible.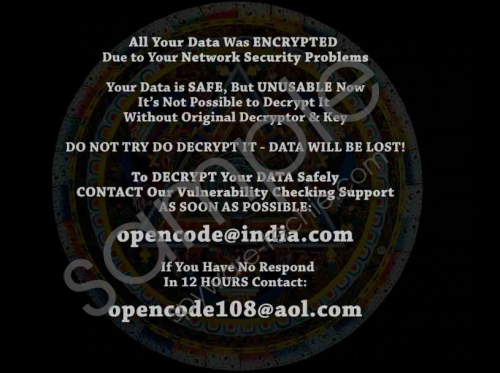 Opencode@india.com Ransomware screenshot
Opencode@india.com Ransomware screenshot
Scroll down for full removal instructions
At any rate, after the encryption is complete, the ransomware will create a ransom note called Decryption instructions.txt and drop it on the desktop and probably in each folder where a file has been encrypted. It will also create a file named Decryption instructions.jpg that is placed in C:\Users\{user name}\ and set it as your PC’s desktop wallpaper. Decryption instructions.txt contains text that says “All of your files are encrypted, to decrypt them write me to email: opencode@india.com , in case of no answer in 24 hours write to alternative e-mail: opencode108@aol.com.” As you can see, the criminals might not always respond to your message, so this begs the question: Will They send the decryption program? alternatively, just keep the money and will not keep their end of the bargain? It can it can go either way, but you should consider the possibility of getting duped by those people.
Our security experts have compared Opencode@india.com Ransomware with the likes of Ecovector3@aol.com Ransomware, Vegclass@aol.com Ransomware, Alex.vlasov@aol.com Ransomware, and Radxlove7@india.com Ransomware and concluded that they are all very similar. This does not come as a surprise because they are all based on the CrySIS ransomware platform and use the RSA-2048 encryption algorithm. Without a doubt, all of them originate from the same developers, and we suspect the criminals responsible for releasing these malicious applications are based in Russia because some of them have their ransom notes written in both English and Russian.
Not much is known about Opencode@india.com Ransomware’s dissemination channels. However, we think that it should be distributed in the same ways as its counterparts. Therefore, we assume that its dropper file is attached to email spam and sent to random email addresses. The malicious email attachment requires you to open it, and if you have, then that is how your computer became infected with this ransomware. Furthermore, some of its predecessors were disseminated using exploit kits featured on infected websites. These kits rely on you to intact with JavaScript and Flash-based content to get your computer infected. However, there is nothing more we can add to this until there is more information.
If you want to get rid of this malware manually, then you can use the guide featured below. However, it requires some know-how, so if you are an inexperienced PC user, then we recommend suing an antimalware application such as SpyHunter, because while performing manual removal, you might accidentally delete the wrong file or registry keys. Take note that Opencode@india.com Ransomware’s executable is named randomly and can be located in three locations in total. So, if you want to play it safe, then get an antimalware tool.
How to remove this malware
- Simultaneously press Windows+E keys.
- Enter each of the following locations in the File Explorer’s address box.
- %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup
- %USERPROFILE%\Microsoft\Windows\Start Menu\Programs\Startup
- %ALLUSERSPROFILE%\Start Menu\Programs\Startup
- %ALLUSERSPROFILE%\Microsoft\Windows\Start Menu\Programs\Startup
- %ALLUSERSPROFILE%\Application Data\Microsoft\Windows\Start Menu\Programs\Startup
- %WINDIR%\System32
- %WINDIR%\Syswow64
- Identify the executable file, right-click it and click Delete.
- Close the File Explorer and Empty the Recycle Bin.
- Then, simultaneously press Windows+R keys.
- Type regedit click OK.
- Go to HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Wallpapers
- Find and delete BackgroundHistoryPath0
- Then go to HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- Find a randomly named two strings whose Value data is %WINDIR%\Syswow64\randomname.exe and %WINDIR%\System32\randomname.exe
- Delete these registry strings.
- Done.
In non-techie terms:
Opencode@india.com Ransomware is one of many malicious applications that have been developed by the same clandestine developer. It is configured to encrypt your files and demand that you ay a ransom, but the sum is not specified. It requires you to contact the criminals via email to get the instructions on how to pay it. Unfortunately, there is no way you can decrypt the files for free since a free decryption tool has yet to be created. So we suggest that you delete it using the guide above or our featured antimalware application.
