Do you know what Newsearch123.com is?
You should be surprised to find Newsearch123.com installed on your browsers if you did not give the permission. Programs that are capable of modifying search settings – especially when it is done without permission – are classified as browser hijackers, and they require removal. This hijacker also requires removal, and this report discusses why this is necessary. The first thing we need to mention before starting the discussion about the program itself is that it could be downloaded along with other unreliable programs. Therefore, if you encounter this hijacker, it is crucial that you immediately scan your operating system to see which other potential threats might have invaded. We will not discuss the removal of Newsearch123.com-related malware in great lengths, but you might be able to find appropriate guides on this site using the search box on the right.
Your browser is your gateway to the web, and a browser hijacker can open security backdoors making your entire experience very precarious. It was found that Newsearch123.com – which is identical to Istartsurf.com, Yoursearching.com, and Mystartsearch.com – can show modified search results, which means that it could expose you to links leading to corrupted websites. Although the search results are shown via Google, they can be modified, and this is why you should stay away from them. Of course, you can choose to ignore this hijacker; however, that is not an option we recommend. First of all, even if you ignore this hijacker, it will continue spying on you using tracking cookies that, of course, require removal as well. According to the Privacy Policy, these cookies to not track personal data; however, that does not mean that other kinds of information cannot be used in a harmful way. For example, your browsing history could be used to expose you to malicious content concealed using attractive offers directly targeted at you. Keep in mind that the programs downloaded along with this hijacker might install their own intrusive tracking cookies.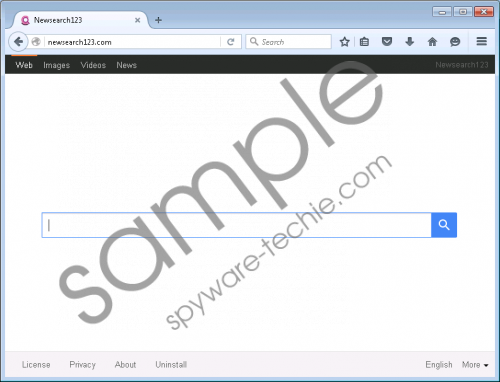 Newsearch123.com screenshot
Newsearch123.com screenshot
Scroll down for full removal instructions
It was found that Newsearch123.com is mostly spread in India, Algeria, Pakistan, Indonesia, Bangladesh, Sri Lanka, and Vietnam; however, it was found in various countries around the world. The IP address of this hijacker is 108.162.204.39, and it is also associated with potentially unwanted programs (e.g., Chroomium Browser, Ghokswa Browser, and Picexa), hijackers (e.g., yessearches.com), and adware. It is likely that these programs require removal, which is another signal that the hijacker we are discussing is not reliable. Although it is unlikely that you will find these suspicious programs bundled with the hijacker, it is obvious that your operating system is susceptible to malware. If you do not protect your browsers and your entire operating system using reliable software, it is unlikely that you will be able to keep malware away. Of course, before you take care of the protection, you have to remove existing threats.
There is no question about whether or not you should remove Newsearch123.com. Of course you should, and we are here to make sure that you delete this hijacker successfully. You can change the settings under HKLM\SOFTWARE\Microsoft\Internet Explorer\Main, or you can change the settings directly on Internet Explorer. The same goes with Firefox and Chrome. If you do not change the settings directly on the browsers, you will have to remove files (under C:\Users\{user name}\AppData\Local\Google\Chrome\User Data\Default and C:\Users\{user name}\AppData\Roaming\Mozilla\Firefox\Profiles\{Unique Mozilla user ID}). Our recommendation for you is to delete the folder found under %AppData% and change browser settings manually, as shown below. If you are not ready to delete third-party malware or defend your Windows operating system against it, employ antimalware software.
How to delete Newsearch123.com
N.B. First go to %AppData%\newsearch123 and delete all files, including the folder that contains them.
Delete from Google Chrome:
- Launch the browser, tap Alt+F, and click Settings.
- Under On Startup select Open a specific page or set of pages and click Set pages.
- Identify the URL representing the hijacker, change/remove it, and click OK.
- Under Appearance select Show Home button and click Change.
- Identify the URL representing the hijacker, change/remove it, and click OK.
- Under Search click Manage search engines and set the desired engine.
- Remove the undesirable search provider and click Done.
Delete from Internet Explorer:
- Launch the browser, tap Alt+T, and click Internet options.
- Click the General tab, change/remove the Home Page URL, and click OK.
- Tap Alt+T one more time and select Manage Add-ons.
- In the menu on the left click Search Providers and set the desired provider.
- Remove the undesirable search provider and click Close.
Delete from Mozilla Firefox:
- Launch the browser, tap Alt+T, and click Options.
- In the General menu change/remove the Home Page and click OK.
- Navigate to the Search menu and Remove the undesirable provider.
- In the list of available providers select the desired one.
In non-techie terms:
Newsearch123.com is a hijacker, and you need to remove it from your operating system. If you do not delete this browser infection, you will have information about you collected, and every single search conducted will expose you to unpredictable content. We have found that this hijacker can be downloaded silently by potentially unwanted programs, in which case, other threats could have been downloaded without permission as well. Hopefully, that is not the scenario you will have to deal with. If it is, it is worth investing in reliable antimalware software to have all threats deleted at the same time. If you do not have skills or experience deleting malware, it might be extremely difficult for you to get rid of all threats manually.
