Do you know what LightningCrypt Ransomware is?
The 25th of May, 2017 is the day when a new ransomware infection LightningCrypt Ransomware was developed and started being actively distributed by cyber criminals. Although it is a new threat, it shares the same goal with older ransomware-type infections – it seeks to obtain money from users. So that it could do that easier, it enters PCs, finds where valuable files are located, and then immediately locks them all. Because of this, even though LightningCrypt Ransomware is spread using deceptive methods of distribution, it does not take long to realize that this malicious application has successfully slithered onto the computer. Are you reading this article because your files have been locked too and a new filename extension .LIGHTNING (e.g. mypicture.jpg.LIGHTNING) has been appended to them? If so, delete this infection as soon as possible without even considering paying money to cyber criminals. We cannot promise that you could decrypt your files if you do not purchase a private key from them, but we can assure you that you could erase this infection from PC yourself.
The name of the LightningCrypt Ransomware launcher is ChkDsk.exe, so some users might open it thinking that it is a tool for checking disks and fixing errors on them. Once this ransomware infection is launched, it changes Desktop background, opens a .txt file with a ransom note, and then launches its main window on Desktop. As mentioned in the first paragraph, it also performs the encryption process. Luckily, it does not encrypt all of them. These are all extensions it targets: .avi, .dll, doc, docx, .dotm, .exe, .jpg, .lnk, .mp3, .mp4, .nef, .odt, .pdf, .pif, .png, .rar, .txt, .url, .wav, and .zip. It locks only these files not without reason – they are considered the most valuable data. Evidently, cyber criminals behind this ransomware infection expect that users will pay money to get those files decrypted without much consideration. The size of the ransom at the time of writing is 0.17 Bitcoin (~417 USD). The amount of money required has to be transferred to the provided Bitcoin address belonging to cyber criminals. The unique user’s ID (it can be found in LightningCrypt_UniqeID.txt left on Desktop) has to be provided in the payment description too. A number of users believe that sending the money required is the quickest solution to the problem, but specialists have a different opinion. According to them, it is the biggest mistake users can make because nobody knows whether they will get the decryption key after making a payment to the author of the ransomware infection. They say that users who back up their files periodically can go straight to delete LightningCrypt Ransomware because they could easily recover their files from a backup after this threat is gone.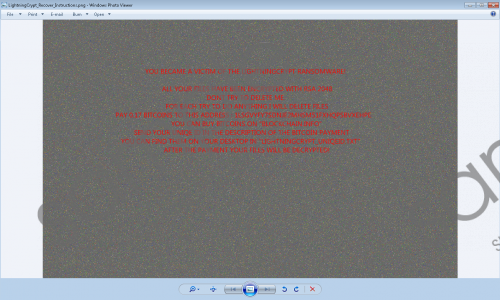 LightningCrypt Ransomware screenshot
LightningCrypt Ransomware screenshot
Scroll down for full removal instructions
If you make a decision not to send a cent to cyber criminals, you still need to delete this ransomware infection from your computer. Those users who do not do anything about its presence might find their files encrypted one more time. In addition, they might suddenly notice that the speed of their Internet connection has decreased. It is because LightningCrypt Ransomware keeps connecting to different domains, e.g. arizonacode.bplaced.net, lolaail.bplaced.net/4rw4w.exe, and rammichael.com.
Despite the fact that LightningCrypt Ransomware is a new ransomware infection, good old distribution methods are used to spread it. First, it might be spread as an attachment in spam emails. Second, it might pretend to be legitimate software on file-sharing websites. As mentioned at the beginning of this article, its file has a name ChkDsk.exe, so some users open it fearlessly because they believe that it is an installer of useful software. It is the main mistake they make. Ignore all unsolicited emails and their attachments in the future and enable security software on your computer to prevent ransomware-type infections from slithering onto your computer once again.
We cannot promise that it will be easy to remove LightningCrypt Ransomware because it is a sophisticated malicious application having a bunch of components that need to be removed. They can all be erased either automatically or manually. Below you will find provided the manual removal guide, but it will be useless if you decide to delete this threat automatically. In this case, you will only need to acquire an automatic tool.
How to delete LightningCrypt Ransomware
Boot into Safe Mode
Windows 8/8.1/10
- Press the Windows key + C on your keyboard and click Settings (Windows 8/8.1) or click on the Start button (bottom-left corner).
- Click Power.
- Hold down the Shift key and click Restart.
- Click Troubleshoot.
- Select Advanced options.
- Click Startup Settings.
- Click on the Restart button.
- Tap F4 on your keyboard.
- Go to remove malicious components of LightningCrypt Ransomware.
Windows XP/Vista/7
- Reboot your computer.
- Start tapping F8 when BIOS starts loading.
- Select Safe Mode using arrow keys and press Enter.
- Go to remove a ransomware infection from your PC.
Remove malicious components
- Tap Ctrl+Shift+Esc.
- Open the Processes tab.
- Kill suspicious processes.
- Open the Windows Explorer (tap Win+E).
- Delete all suspicious files from %TEMP%, %USERPROFILE%\Downloads, and %USERPROFILE%\Desktop directories (enter the directory in the Windows Explorer’s address bar to open it).
- Close the window and press Win+R.
- Enter regedit.exe and click OK.
- Move to HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run.
- Delete entries representing LightningCrypt Ransomware.
- Close the Registry Editor.
- Remove three files from Desktop: LightningCrypt_Recover_Instructions.txt, LightningCrypt_UniqeID.txt, and LightningCrypt_Recover_Instructions.png.
- Empty the Trash bin and reboot your computer.
In non-techie terms:
Ransomware infections are threats which always cause a bunch of problems, so if you have become a victim of this infection once, it means that it might sneak onto your computer and cause trouble the next time too if you do not do anything to ensure the maximum protection of your system. Security specialists say that there is one easy way to prevent undesirable software from illegally sneaking onto the system – users need to go to install trustworthy security software on their computers and enable it.
