Do you know what Last_centurion@aol.com Ransomware is?
Last_centurion@aol.com Ransomware is designed to enter computers without permission. Even though it sneaks onto computer secretly, it does not try to stay unnoticed. Instead of hiding deep on the computer and working behind a user’s back, it immediately encrypts personal files it finds after the system scan. Our team of specialists has made a conclusion that Last_centurion@aol.com Ransomware encrypts the most valuable data, i.e. files having the following extensions (an incomplete list): .jpg, .mp3, .wav, .ppt, .tif, .html, .php, .docx,.doc, .pptx, .3GP, .avi, .ico, .cfg, .vcf, .7z, .txt, .svg, .eps, .xlr, .accdb, and .rom. To decrypt objects having the extension .id-(unique ID).{Last_centurion@aol.com}.xtbl (files locked by the ransomware infection have this extension), you will have to pay money to cyber criminals. To be honest, cyber criminals encrypt files because they seek to get money from users. You are the only one who can make decisions here; however, if you are curious to know what experienced specialists think, you should know that they are strictly against making payments for cyber criminals. Our researchers also suggest getting rid of Last_centurion@aol.com Ransomware as soon as possible because this infection might not only encrypt other files you create in the future, but might also help malicious applications to enter the system. Read the article to find out how quickly and easily to delete Last_centurion@aol.com Ransomware.
To be able to encrypt files and act the way it is programmed to, Last_centurion@aol.com Ransomware places its executable file on the system the second it finds a way to enter the computer. If you are a more experienced user, you will notice several other modifications in the system registry as well. One of these well noticeable changes is the presence of the new Value in HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run. It is placed there so that the ransomware infection could launch automatically when the Windows OS loads up. Do not worry; these changes can be undone. You just need to delete the ransomware infection from your computer. You can find more information about the deletion of this threat in the last paragraph.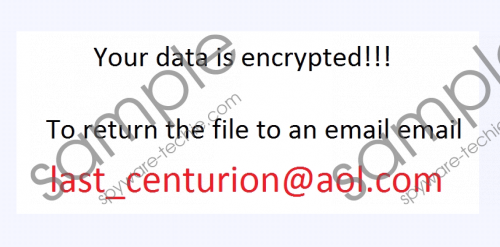 Last_centurion@aol.com Ransomware screenshot
Last_centurion@aol.com Ransomware screenshot
Scroll down for full removal instructions
The executable file is not the only one the ransomware infection creates on the infected computer. Once Last_centurion@aol.com Ransomware finishes encrypting personal files, it changes the wallpaper and creates the .txt file (Decryption instructions.txt) on Desktop. It contains the following message inside:
All of your files are encrypted, to decrypt them write me to email: Last_centurion@aol.com. In case of no answer in 24 hours, write to Last_centurion@aol.com
Users find out what has happened to their files that they cannot access them, but they are not explained much about the decryption process. Therefore, we believe that cyber criminals send further instructions when people write an email to them. Even though we have not tried contacting cyber criminals, we are sure that cyber crooks ask users to pay money for the decryptor. You should not transfer money even if you find the decryptor affordable because it is very likely that you will not get anything from cyber criminals, i.e. the decryptor will not be sent to you and, of course, the refund will not be issued.
There are several different ways how file-encrypting ransomware infections are distributed, for example, they might be introduced to machines by the Trojan-Dropper, or you might get its executable file from a third-party website. Researchers have managed to find out that ransomware infections are distributed though spam emails as well. To be frank, this is the most popular way of ransomware distribution. Never open these spam emails despite the fact that they seem to be harmless. Actually, there is not much you can do to protect the system from malware by yourself, so we suggest installing security software on the computer as well. You can get the free version of SpyHunter, which is a reliable antimalware tool, from spyware-techie.com.
There is no need for you to delete Last_centurion@aol.com Ransomware manually because there is a tool, i.e. SpyHunter that can erase this infection for you within seconds; however, if you are still eager to remove it by yourself, use the manual removal guide you will find if you scroll down. It will not be easy to get rid of the ransomware because its files have random names.
Remove Last_centurion@aol.com Ransomware manually
- Launch Run (press Win+R).
- Enter regedit and click OK.
- Open HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run and delete the random name Value that belongs to the ransomware infection.
- Move to HKCU\Control Panel\Desktop.
- Right-click on the Wallpaper Value, select Modify, and then clear the Value data. Click OK.
- Empty the Value data field (refer to the 5th step of this guide) of the BackgroundHistoryPath0 Value which can be found by following this path HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Wallpapers as well.
- Delete the {randomname}.exe file that belongs to the ransomware. It can hide in any of these directories:
- %WINDIR%\Syswow64\
- %WINDIR%\System32\
- %ALLUSERSPROFILE%\Start Menu\Programs\Startup\
- %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\
- %USERPROFILE%\Microsoft\Windows\Start Menu\Programs\Startup\
- %ALLUSERSPROFILE%\Microsoft\Windows\Start Menu\Programs\Startup\
- %ALLUSERSPROFILE%\Application Data\Microsoft\Windows\Start Menu\Programs\Startup\
In non-techie terms:
If the ransomware infection has found a way to enter your PC, there is a small possibility that other computer infections have sneaked onto your computer secretly too. You might not know that they are inside your system because they often work silently behind a user’s back. It is possible to find threats manually, but it is a really long process. Also, a user must be experienced. If you are not one of them, scan your system with a free diagnostic scanner. You can get it from this web page.
