Do you know what Kill Imme is?
Kill Imme seems to be a new variant of a malicious file-encrypting program called Xorist Ransomware. Users can recognize it from the way the infection marks its damaged files since it adds either .imme.teras.completecrypt or .imme extension. The malware should also drop a text document with the message from the threat’s developers in each folder that contains encrypted files. The data it enciphers might be locked with a secure cryptosystem. Therefore, at the moment the only way to unlock such files might be using a decryption tool created for Xorist Ransomware by volunteer IT specialists. However, there are no guarantees such decryptor could work, so it might be best to try the tools only on a couple of files or better yet on their copies. If you wish to know more about Kill Imme we recommend reading the rest of the text. As for users who want to eliminate the malware faster, we advise sliding below the text as there you can find a removal guide.
According to the infection’s developers, Kill Imme locks “important personal files.” Such data could be the user’s text files or other documents, pictures, photos, videos, and so on. It is important for the threat’s creators that you would be able to open the text document they create and read the provided message, which means all data belonging to the operating system or perhaps even other software on the computer might be left unencrypted. Our researchers say the ransom note should appear in every directory containing locked data. The message in it says “TO RESTORE YOUR FILES YOU HAVE TO PAY 2 BITCOINS.” At the moment of writing, it is approximately 2,344 US dollars.
Moreover, the message instructs users to contact the hackers via particular email addresses (supfiles@inbox.im or supfiles@gmx.com) after making the payment. Apparently, to fulfill this request, you have only 72 hours because after the time runs out, it is said the price could increase. It seems to us the price asked for the decryption tool is enormous already as it is; thus, we advise against paying it. The malware’s creators may not bother to help you with decryption once the payment is made and if you find yourself in such situation, you could lose not only personal data but also the transferred money as it would be impossible to get them back. Users who do not want to take any chances might try to use the decryption tool we mentioned at the beginning of the article. On the other hand, you could simply replace damaged files with copies, provided you had made any before the computer was infected. Of course, it would be safer to delete Kill Imme first. After all, there is no point in keeping the malware.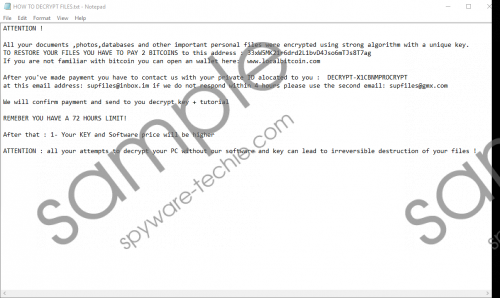 Kill Imme screenshot
Kill Imme screenshot
Scroll down for full removal instructions
We could suggest two option for dealing with Kill Imme. Firstly, you could try to locate data related to it on your own and erase it manually. To assist our readers with this task, we placed a step by step removal guide just below the text. Needless to say, this option might be too difficult for some users, so it might be best to employ a legitimate antimalware tool and let it delete the infection for you. Keeping such a tool could be beneficial for the system as it would allow you to remove other possible threats and help you guard the system against malicious programs you may yet encounter.
Get rid of Kill Imme
- Press Windows Key+E.
- Insert the listed paths one by one:
%TEMP%
%USERPROFILE%\desktop
%USERPROFILE%\downloads
%APPDATA%
%LOCALAPPDATA% - Look for suspicious files that could be related to the malware; their titles might be random.
- Right-click the files you suspect to be malicious and press Delete.
- Close the Explorer.
- Empty the Recycle bin and restart the computer.
In non-techie terms:
Kill Imme is a malicious application programmed to encipher your data or in other words, take it as a hostage. The malware’s creators expect their victims to pay a ransom of more than two thousand US dollars, so we advise users not to risk with their savings. The infection’s creators may promise you anything to convince you to make the transfer, but there are no guarantees they will be willing to send you the decryption key they promise. Instead of trusting these people, we would advise our readers to eliminate the malicious program and try alternatives way to recover damaged data, e.g. backup files, copies on removable media devices, and so on. You can erase the infection manually with the removal guide placed above or automatically with reputable antimalware software.
