Do you know what Globasearch.com is?
Globasearch.com is a domain that is set as your homepage when you get infected with a browser hijacker. It takes over your browser and monitors your web browsing sessions to collect information on your web browsing habits. It is highly intrusive and malicious, especially as the information collected by this program can be easily leaked to associated third parties. You will do yourself a favor if you remove Globasearch.com immediately. Resetting your browser settings to default may not be enough to terminate all the potential threats, so please consider investing in a licensed computer security tool.
When this browser hijacker enters your computer, it affects your default browser at once. Globasearch.com is known to be compatible with Internet Explorer, Mozilla Firefox, and Google Chrome. Thus, after the infection, the next time you open your browser, your default homepage will be changed to Globasearch.com. It is definitely rather annoying, but that is not all there is to this program.
Usually, the domain that is used for the homepage is the same that a browser hijacker uses to set as your default search engine as well. However, in the case of Globasearch.com the story is slightly different. There is an entire list of search engines that can be added to your browser, including safe-web.tk, search-eyes.tk, fast-search.tk, and so on. All of these websites supposedly provide you with a user-friendly search function, along with various shortcuts to Wikipedia, YouTube, Yahoo, and other popular pages.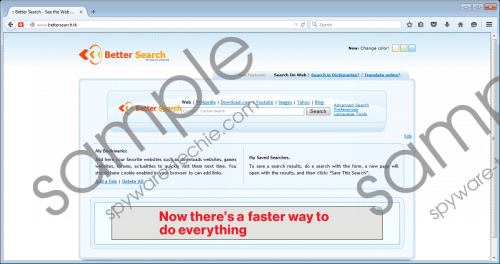 Globasearch.com screenshot
Globasearch.com screenshot
Scroll down for full removal instructions
Truth be told, all of the search engines used by Globasearch.com are practically identical, save for the varying design. What’s more, each search engine has enough of advertising space to tell that they can be used for third-party content promotion. This means that there is a possibility to get exposed to corrupted content accidentally. Of course, if you do not click anything, nothing will happen, but users have a tendency to click random links and flashing advertisements without giving it a second thought.
We would strongly suggest that you NEVER do that. What’s more, you should never click the search result links provided by Globasearch.com. Take note that all of your search queries are being redirected through a customized Google search engine, so you can be sure that most of the results will be related to some promotional campaign. What’s more, it only proves that neither Globasearch.com nor any of its search domains are genuine search engines that can provide you with reliable search service.
To take everything into account, Globasearch.com is a dangerous computer infection that is not associated with any particular program. It means that the hijacker could be hiding anywhere, and it is a lot easier to get infected with it than you think. If you happen to have this program on your computer, you should run a full system scan to detect all the files associated with the infection. It may not be possible remove them manually, so it is always a good idea to invest in a computer security tool of your choice.
Aside from removing everything related to Globasearch.com from your computer, a computer security program will help you protect your system from similar intruders in the future. Just do not forget to turn on the automated updates function, so that your security tool would always be updated to the latest version.
How to Restore Your Browser Settings to Default
Google Chrome
- Press Alt+F and click Settings.
- Scroll down and click Show advanced settings.
- Scroll down to the bottom and press Reset Settings.
- Click Reset.
Internet Explorer
- Press Alt+T and click Internet options.
- Open the Advanced tab and click Reset.
- Mark the Delete personal settings option.
- Click Reset and press Close.
Mozilla Firefox
- Press Alt+H and click Troubleshooting information.
- When the new tab opens, click Refresh Firefox.
- Press Refresh Firefox on the confirmation box.
- Click Finish.
In non-techie terms:
Globasearch.com is a corrupted website that appears on your web browser. The presence of the domain means that you have been infected with a browser hijacker. You need to remove Globasearch.com from your browser to protect yourself from even more serious infections. For an alternative software and malware removal method, please refer to the secondary set of instructions below this description.
