Do you know what Explorer Ransomware is?
There are three main symptoms showing that the arrival of Explorer Ransomware on your system was successful. First, there is a new image set as Desktop background. Second, it is impossible to access the majority of files. Third, a new file READ_IT.txt can be found on Desktop. Research has shown that ransomware infections usually enter computers illegally, but we would lie if we said that users have nothing to do with that. In most cases, they are the ones who trigger the installation of malware. For example, they might click on a fake Download button, open a malicious attachment, or download malware pretending to be useful software from the web. No matter how Explorer Ransomware has slithered onto your computer, you must delete it from the system. Unfortunately, your files will not be unlocked even if you fully erase this HiddenTear-based ransomware infection. This does not mean that you could not get your files back. There is one way to do that – to restore them from a backup. Do this only after you erase this infection because it might strike again.
It does not take much time to realize that Explorer Ransomware is inside the system because it starts working right after the successful entrance. First, it scans the system and finds where pictures, documents, text files, and other valuable files are stored. Then, the encryption procedure takes place and all files receive a new extension .explorer. If victims do not notice a new extension appended to files, they definitely notice a new image set as Desktop background and a new .txt file READ_IT.txt on Desktop. They both contain the same text. Users find out that their “documents, photos, databases and other impotant personal files were encrypted by a strong algorithm with unique key.” Also, they find out that the only way to unlock those encrypted files is to write an email to decrypter.files@mail.ru and pay a ransom. Writing an email to cyber criminals and paying money to them might seem to be the easiest way to get files back, but we still do not recommend transferring a ransom because nobody knows whether you will receive a decryption tool after doing that. As mentioned in the first paragraph of this article, there is a way to restore files without the special tool. The only thing you need to have to do this is a backup.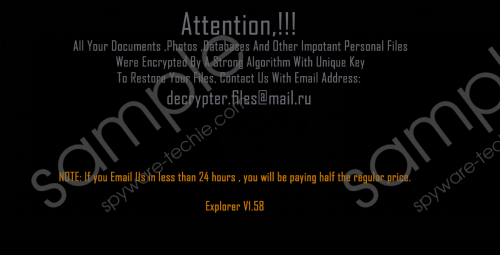 Explorer Ransomware screenshot
Explorer Ransomware screenshot
Scroll down for full removal instructions
It is not easy to talk about the distribution of Explorer Ransomware because there are several distribution methods actively used to spread ransomware infections. Of course, there is one tactic used more frequently than others. It has been found that ransomware-type infections are primarily distributed via spam emails. In some cases, they even pretend to be important documents to make sure that users open them and they can enter their PCs without many difficulties. Since ransomware infections are sneaky and several different methods are used to spread them, the chances are high to encounter such a threat. Because of this, you must ensure your system’s maximum protection today.
Although your files will stay as they are, i.e. locked, you must delete the ransomware infection from your computer as soon as possible. It will disappear from your system if you delete all recently downloaded suspicious files and remove READ_IT.txt from Desktop. If you have never deleted malware before and do not have much knowledge about the deletion of malicious software, you should consult our manual removal guide. It will help you to delete the ransomware infection fully from the system without leaving a single malicious component active.
How to delete Explorer Ransomware
- Open Windows Explorer.
- Go to delete all suspicious recently downloaded files from your computer (they are usually located in %USERPROFILE%\Desktop and %USERPROFILE%\Downloads).
- Remove READ_IT.txt from Desktop.
- Empty Recycle bin.
In non-techie terms:
Explorer Ransomware is a nasty infection whose main purpose is to lock users’ files and then obtain money from them. All ransomware infections seek to extract money from users, so make sure they cannot enter your PC and cause harm. Your will protect your system from dangerous computer infections by installing security software on your PC. Only trustworthy tools can prevent malware from entering your PC, so do not install the first scanner you come across on some kind of file-sharing website – the chances are high that such a tool will be useless.
