Do you know what CryptoViki Ransomware is?
Our malware analysts have recently tested a new ransomware called CryptoViki Ransomware. This program was first seen at the beginning of May 2017 and has been distributed ever since. Like most ransomware-type infections, it was configured to encrypt your personal files with an advanced encryption algorithm and demand that you pay a ransom to get them back. However, you cannot trust the developers to keep their end of the bargain and send you the decryption key. Therefore, we recommend that you remove this program from your PC and try to recover your files from backup drives.
Ransomware, in general, is on the rise as it is now more sophisticated and widely distributed. If this particular program enters your PC, then it will start encrypting your files right away. It uses a combination of RSA and AES encryption algorithms to render your files inaccessible. This ransomware does not change the names of the encrypted files but appends them with a “.viki” extension. Note that this ransomware will encrypt your files in all internal external and removable drives. We do not have a list of encrypted file extensions, but testing has shown that it is set to encrypt most file extensions. However, it skips some locations in order not to damage the operating system and other crucial programs.
Once the encryption is complete, CryptoViki Ransomware drops a file named “wallpaper.jpeg” that is set to replace your desktop wallpaper. The image features text that says that all your disks have been encrypted and that the details are in another file named “readme.txt.” The text is both in English and Russian, so we assume that it was developed in Russia or some other Eastern European country. The file "readme.txt" features information such as the email address of the developers, and you need to message them to get instructions on how to pay the ransom and get the decryption key. Furthermore, the note warns you not to decrypt the files using a third-party tool as it can irreversibly damage the files. However, the trust is that a good decryption tool could get you your files back, but the problem is that there currently is not third-party decryption tool capable of decrypting the cipher of this ransomware.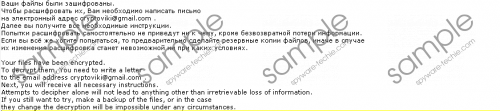 CryptoViki Ransomware screenshot
CryptoViki Ransomware screenshot
Scroll down for full removal instructions
Now let us talk distribution. Apparently, since CryptoViki Ransomware is relatively new, there is not enough information to determine how exactly it is distributed. All we know is that is it most likely to be distributed using email spam. However, we do not know anything further than that. Regardless, there are a few plausible scenarios to discuss. The emails can either contain a link to this ransomware’s direct download, or it might feature the main executable as an attached fake Word or PDF document. The executable can be zipped and have a double extension to trick users into thinking that it is a .doc, docx, or .pdf file. Depending on the infection method, you can extract this file manually if it is zipped or it might be hidden if it is downloaded via a link. Therefore, you might need an anti-malware program to detect it.
We hope you found this article insightful. As you can see, CryptoViki Ransomware is one dangerous computer infection that can enter your PC secretly and encrypt most of your files. However, you should not trust its developers to give you the decryption key after you have paid because you might get scammed. You can use SpyHunter to detect the malicious file and delete it manually or use this same program to remove it as well.
Delete CryptoViki Ransomware manually
- Go to http://www.spyware-techie.com/download-sph
- Download SpyHunter-installer.exe and run it.
- After installing it, select Scan Computer Now!
- Note the file path of the ransomware.
- Press Win+E keys while in desktop.
- Enter the file path in the File Explorer’s address box and hit Enter.
- Right-click the malicious executable and click Delete.
- Delete wallpaper.jpeg and readme.txt
- Empty the Recycle Bin.
In non-techie terms:
Our malware analysts have concluded that Delete CryptoViki Ransomware is a highly malicious computer infection that can secretly infect your computer via email and encrypt many of your personal files. Unfortunately there is no free decryption tool, but paying the ransom is not an option because the criminals might not keep their end of the bargain. Therefore, we suggest that you remove it using our guide.
