Do you know what Crypton Ransomware is?
Crypton Ransomware is one of the most dangerous infections. It has been recently detected by our team of specialists, and it seems to be targeting people speaking Russian or English. In other words, its purpose is to affect thousands of computers. Ransomware infections enter computers to encrypt users’ files mainly. Once they finish doing that, they demand a ransom. Crypton Ransomware is no exception. It has been found that it encrypts all the files by appending the .crypt extension to all of them the moment it is inside the system. After doing that, it opens the so-called ransom note. It becomes clear after reading it that Crypton Ransomware also seeks to extort money from users. Since the C&C server it uses is down at the time of writing, it is impossible to say what the size of the ransom is, but it is very likely that the amount of money asked is considerable. Keep in mind that you might be left without your files and without your money too, so you should better focus on the Crypton Ransomware removal rather than the transfer of money to cyber criminals.
Our researchers have revealed that Crypton Ransomware uses the AES algorithm to encrypt files. This threat uses such a strong encryption algorithm not without reason. Cyber criminals perfectly know that it will be very hard to decrypt files ciphered with it. To be frank, it might be impossible to unlock files. This means that you will lose files having the following filename extensions: 7z; .cd; .cdr; .dat; .db; .dbf; .dbx; .doc; .docx; .htm; .html; .jpg; .mdb, .mht, .pdf, .png, .ppt, .pptx, .psd, .pst; .rar, .rtf, .tbb, .tbn, .tiff, .txt, .vsd, .xls, .xlsx, .xml, and .zip. Of course, we do not say that you should give up immediately. Users who are not going to transfer money to cyber crooks (it is not recommended to do that since the C&C server is down and cyber criminals might not even bother unlocking files after receiving money) should download several reliable free data recovery tools from the web and try them out. If shadow copies of files are not deleted by the ransomware infection, it might be possible to recover them. Before you do that, remove Crypton Ransomware because it is still active on your PC and might encrypt your recovered files once again.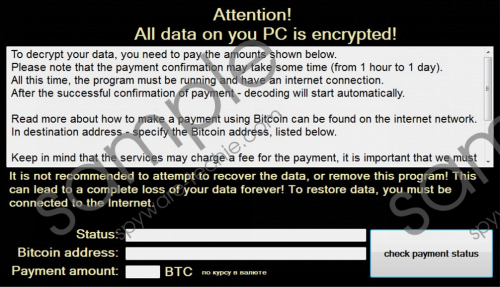 Crypton Ransomware screenshot
Crypton Ransomware screenshot
Scroll down for full removal instructions
Let’s talk about other changes Crypton Ransomware makes when it enters the system. First of all, our researchers have found that this infection drops the executable file to the directory %APPDATA% after the entrance. Secondly, it creates its own registry key HKCU\Software\Crypton. Finally, it creates the Value pointing to the file located in %APPDATA%. This Value can be found in the Run registry key (HKCU\Software\Microsoft\Windows\CurrentVersion\Run). This threat places it there not without reason. This modification is made so that it could launch after the restart or the shutdown of the computer.
It is no longer a mystery how ransomware infections enter computers. It has been found that these threats always enter computers illegally, but users help them (of course, they do not know about that). In most cases, ransomware infections enter computers when users open attachments they find in spam emails. If you have done that too, it is not surprising why your all files have been locked by Crypton Ransomware. Of course, specialists do not say that these threats cannot find other ways to enter computers too. Therefore, according to them, it would be smart to install a reliable security application on the computer to protect the system from similar threats. Do not postpone the installation of the security tool!
Your files will not be unlocked, but you still have to delete Crypton Ransomware fully as soon as possible if you do not wish to find your new files encrypted. If you are planning on deleting this infection manually, do not hesitate to use our manual removal guide. It will guide you through the entire removal process.
Delete Crypton Ransomware
- Press Win+E.
- Copy and paste %APPDATA% in the URL bar to open this directory.
- Find the crypton.exe file and delete it.
- Close the Explorer and press Win+R.
- Type regedit.exe in the box and click OK.
- Right-click on the registry key HKCU\Software\Crypton and select Delete.
- Move to HKCU\Software\Microsoft\Windows\CurrentVersion\Run.
- Locate the Value crypton.
- If it has the Value data pointing to the file located in %APPDATA%, delete it.
- Remove the malicious file launched.
In non-techie terms:
It does not mean that your computer is safe if you have removed Crypton Ransomware from your PC because other infections might still be working on it. They might help other infections to sneak onto the computer, so it is very important to find and delete them all as soon as possible. Since it might take several hours to find them, and it is not always easy to erase them, you should scan your computer with an automatic malware remover, e.g. SpyHunter. Of course, you do not need to launch it again if you have erased Crypton Ransomware with it because it has already taken care of those other infections as well.
