Do you know what Batman_good@aol.com Ransomware is?
Batman_good@aol.com Ransomware is a threat that can attack the computer when you least expect it. Our researchers suspect that the malware might be distributed with malicious email attachments. The worst part is that you may not understand what happened for some time after you open an infected file. Such threats often work silently until they encrypt targeted user’s data. Only then they announce about their presence. If Batman_good@aol.com Ransomware encrypted your files, it is time to learn more about the malicious program. Thus, we recommend reading the rest of the text and if you want to eliminate the threat, have a look at the removal guide below the article.
The executable files that Batman_good@aol.com Ransomware may travel with could look like pictures, text documents, invoices, and so on. Therefore, often users do not expect such data to be malicious. It is even harder to separate suspicious files if you constantly receive various documents through email. Nevertheless, there are a couple of details that should alert you.
Even though users may be used to the fact that sometimes even the emails they expect to receive are classified as spam, it is still better to be extra careful with this category. Especially, if they carry any attachments. Also, it is important to identify the sender and if it is not someone you are familiar with, perhaps it would do no harm to scan the attached file with a reliable antimalware tool? Probably, it would take only a minute to examine it, and you could instantly know if it is infected.
There are ransomware infections that install itself on the system but delete itself too after they encipher the targeted data. However, in this case, Batman_good@aol.com Ransomware does not remove itself, and it places quite a lot of data on the system. Mostly, this malware creates executable files, which are given random titles. Moreover, the malicious application could also make new or modify already existent value names on a couple of keys in the Windows Registry.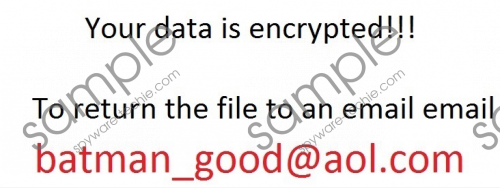 Batman_good@aol.com Ransomware screenshot
Batman_good@aol.com Ransomware screenshot
Scroll down for full removal instructions
Afterward, the infection should lock your private data, such as photographs, videos, audio files, etc. The locked files are appended with an additional extension that might be unique for each user, e.g. picture.jpg.id-C9123127.batman_good@aol.com.xtbl. What’s more, it is possible that the malware could encrypt some data, which belongs to the third-party software installed on your computer. To be more accurate, we are talking about programs created by other companies than Microsoft. For example, if you were using Google Chrome, the browser should crash after the encryption, and it would be impossible to launch it again too.
Once the malicious program finishes enciphering data, it might replace default Desktop image with a picture of its own. This picture serves as a random note as it has text on it. The single line in the image says that to decrypt locked data, the user should contact Batman_good@aol.com Ransomware’s developers via email. They would probably demand you to pay a particular amount of Bitcoins in exchange for a promise that the decryptor will be sent as soon as the money reaches the cyber criminal’s account. Sadly, there is a chance that it will never happen and in this case, you would lose the transferred money. Therefore, we advise users to think this through and consider the risks before making a decision.
Those who do not want to deal with the cyber criminals and care about their systems safety should get rid of Batman_good@aol.com Ransomware. To assist users in this matter, we prepared a removal guide that will help erase the malware manually. If you think you can handle it, slide below the text and follow the provided instructions. Users who do not have much experience could install a trustworthy antimalware tool. It should be easy to use since you only need to click the scanning button and when the report with detections shows up, you can erase all threats by pressing the deletion button.
Eliminate Batman_good@aol.com Ransomware
- Launch the Explorer (Win+E) and go to the listed locations separately:
%ALLUSERSPROFILE%\Start Menu\Programs\Startup
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup
%USERPROFILE%\Microsoft\Windows\Start Menu\Programs\Startup
%ALLUSERSPROFILE%\Microsoft\Windows\Start Menu\Programs\Startup
%ALLUSERSPROFILE%\Application Data\Microsoft\Windows\Start Menu\Programs\Startup
%WINDIR%\Syswow64
%WINDIR%\System32 - Check all of these directories and find executable files with random titles, right-click them one by one and press Delete.
- Close the Explorer and open Registry Editor (press Win+R, type regedit and click OK).
- Locate this particular path HKCU\Control Panel\Desktop and look for a value name titled as Wallpaper.
- Right-click the Wallpaper, press Modify and instead of “How to decrypt your files.jpg” type a title of a picture you prefer.
- Find this directory HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Wallpapers and search for a value name titled as BackgroundHistoryPath0.
- Right-click the BackgroundHistoryPath0, select Modify and replace “How to decrypt your files.jpg” with another picture.
- Go to the given location HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run and find value names that are with random titles (their value data should point to %WINDIR%\Syswow64\*.exe, %WINDIR%\System32\*.exe).
- Select these value names separately, right-click them one by one and press Delete.
- Close the Explorer, right-click the Recycle Bin and select Empty Recycle Bin.
In non-techie terms:
Batman_good@aol.com Ransomware is a threat that could be traveling with infected files, which may be disguised to look harmless. Thus, the malicious program comes uninvited and installs itself without any permission. Still, there is no need to panic as there are a few ways to eliminate it. For example, you could delete it manually with the instructions above or use an antimalware tool. As for encrypted data, it can be recovered if you have any copies of it on removable media devices, cloud storages, social media accounts, etc.
