Do you know what Anony.killers@protonmail.com Ransomware is?
Anony.killers@protonmail.com Ransomware is a malicious piece of software that appears to have been created for testing purposes. Every now and again, we encounter a ransomware that does not work properly, or that does not encrypt files the way it is supposed to. In most cases, these threats do not spread in the wild, and users do not need to worry about them. That being said, the creators of these threats could upgrade them to function as normal ransomware infections, which is why it is so important to talk about them. Of course, if this ransomware has invaded your operating system, there are two things you need to focus on: How will you decrypt your files and how will you delete the infection? Hopefully, you manage both of these tasks successfully, and, when you do, you also protect your operating system reliably to ensure that no other threat can invade it in the future. If you are confused about the decryption of files, as well as the removal of Anony.killers@protonmail.com Ransomware, please keep reading.
Although there are plenty of infections that use the “protonmail.com” service – a few of them include Recuperadados@protonmail.com Ransomware and Santa_helper@protonmail.com Ransomware – we do not know which other infections (if any) the creator of Anony.killers@protonmail.com Ransomware is responsible for. The names of these threats, of course, derive from the email addresses that are used for communication. Once the ransomware slithers in and encrypts files, it also displays a message indicating that you need to contact cyber criminals at one of the given emails. Needless to say, in our case, the email address is “anony.killers@protonmail.com,” and it is represented via a pop-up window entitled “You are fucked.” According to the message in this window, you need to email the given address to have your files decrypted. Obviously, the act of emailing does not actually lead to decryption. Instead, it gives the cyber criminals an opportunity to introduce you to ransom demands. At the time of analysis, the threat was only capable of encrypting files in the “DemoEnryption” folder, which means that it did not encrypt personal files. However, if your personal files are hit, you might consider paying the ransom.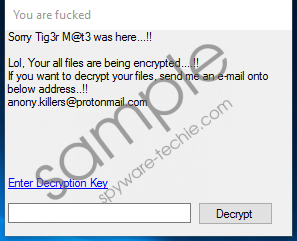 Anony.killers@protonmail.com Ransomware screenshot
Anony.killers@protonmail.com Ransomware screenshot
Scroll down for full removal instructions
According to our research, Anony.killers@protonmail.com Ransomware targets Windows operating systems starting with the Windows Vista version. It does not lock the computer's screen like other ransomware infections can do, and it does not create a point of execution, and that means that it does not start working again after you restart the computer. If the threat does not encrypt personal files, this does not matter; however, if it is capable of encrypting your photos, media files, and important documents (they should have the “.anon” extension attached to them), you do not want to restart the computer. That is because you might not be able to launch the message created by the developer of the ransomware yourself, and that might reduce your options. While we do not recommend contacting cyber crooks and paying the ransom, you want to have all options open. Why paying the ransom is a terrible idea? Because it is highly likely that cyber crooks would take the money without producing the decryption key in return.
Hopefully, no one faces Anony.killers@protonmail.com Ransomware because there are already tons of other threats that can put your virtual security and personal data at risk. If you do encounter this threat, and it has encrypted your personal files, we suggest looking for a third-party decryptor that maybe could decrypt your personal files for free. Also, deleting Anony.killers@protonmail.com Ransomware is very important, and you should not postpone this task for another moment. The instructions below are pretty vague because the infection itself is vague. Its launcher has a random name, and the location is unknown as well. If you have downloaded and executed the file yourself, it will be easier for you to find and remove it. If you cannot clear your operating system manually, employ an anti-malware tool ASAP.
Remove Anony.killers@protonmail.com Ransomware
- Launch Task Manager by tapping Ctrl+Shift+Esc.
- Click the Processes tab.
- Select the malicious process (its decryption should say Encryption) and click End process/task.
- Launch Windows Explorer by tapping keys Win+E.
- Enter %TEMP%, %USERPROFILE\Downloads, or %USERPROFILE\Desktop into the bar at the top (one of these directories might host the malicious launcher file).
- Right-click the malicious .exe file and choose Delete.
- Empty Recycle Bin and then scan your operating system for leftovers.
In non-techie terms:
If your operating system was invaded by Anony.killers@protonmail.com Ransomware, you might find that your personal files have the “.anon” extension attached to their names. If that is the case, these files are encrypted. Paying the ransom that the creator of the ransomware will demand from you at some point is not a good idea because the chances of you getting a decryptor in return of a ransom are very very slim. Hopefully, you can employ a free file decryptor to have your files freed. Of course, we hope that this threat does not invade your operating system at all, or, if it attacks, it does not encrypt your files. The guide above shows how to delete Anony.killers@protonmail.com Ransomware manually, but we suggest employing anti-malware software instead because after successfully eliminating the threat, it will ensure that your operating system is guarded against all threats in the future.
